The escalating threat of physical security breaches necessitates a proactive and systematic approach to risk management. A robust Physical Security Risk Assessment Report Template provides a structured framework for identifying vulnerabilities, evaluating potential threats, and developing effective mitigation strategies. This template is designed to be adaptable to various environments and organizational needs, ensuring a comprehensive understanding of security risks and a prioritized plan for improvement. It's more than just a document; it's a tool for informed decision-making and continuous security enhancement. This report will guide you through the key steps involved in creating a valuable assessment, ultimately bolstering your organization's overall security posture. Physical Security Risk Assessment Report Template is your key to safeguarding assets and personnel.
The initial stages of a successful risk assessment are crucial. It's not enough to simply identify potential threats; you must understand their likelihood and potential impact. A well-crafted Risk Assessment Report Template provides the foundation for this understanding. It's a living document, requiring regular updates and revisions as circumstances change. Consider this template as a starting point – tailoring it to your specific organization and its unique environment is paramount. The goal is to move beyond reactive measures and embrace a culture of continuous security awareness. Investing in a robust Risk Assessment Report Template is an investment in the long-term security of your organization.
Section 1: Defining Scope and Objectives
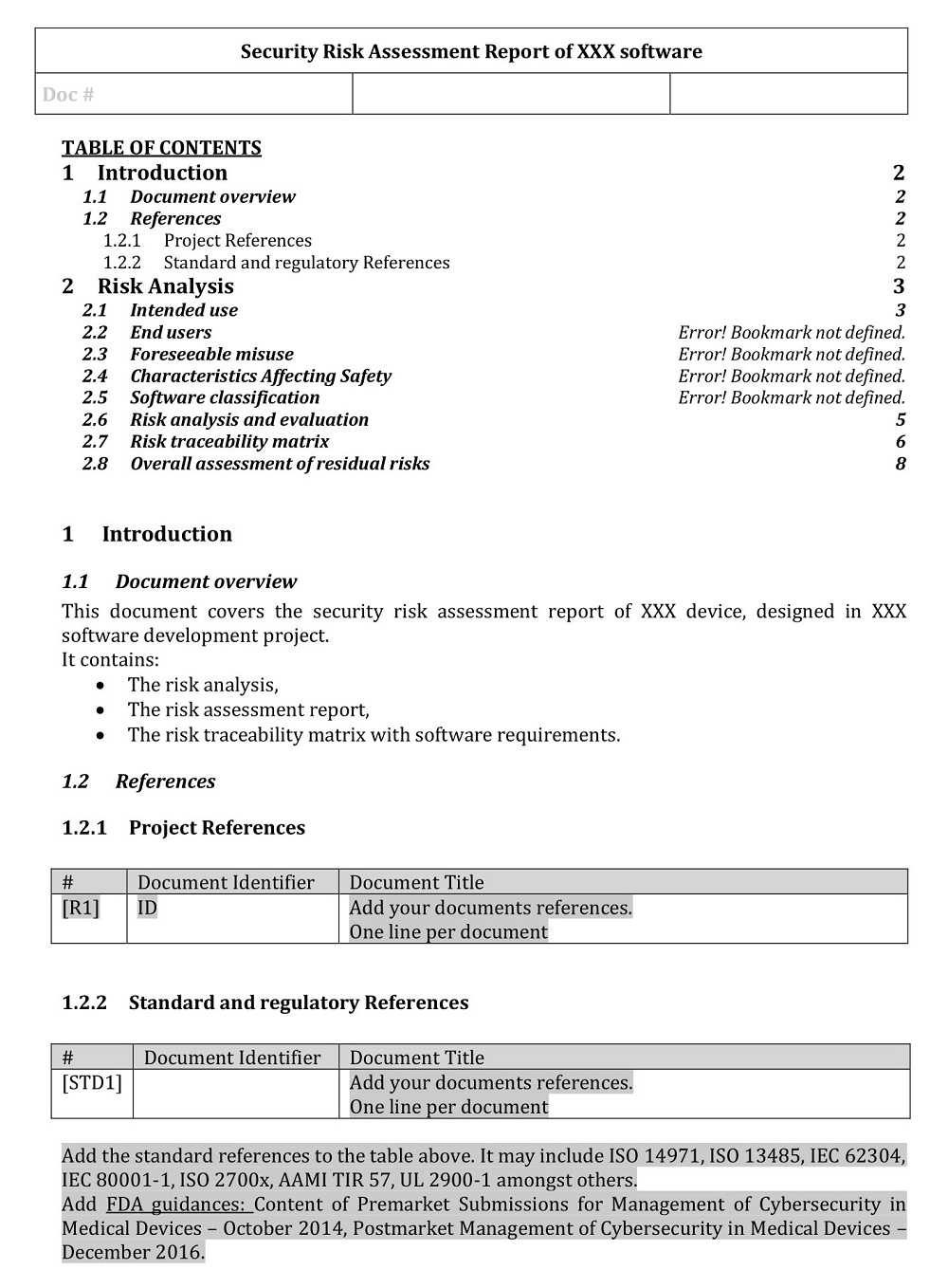
Before diving into detailed assessments, it's vital to clearly define the scope of the risk assessment. This includes identifying the specific assets, locations, and processes that will be included in the evaluation. A clearly defined scope prevents analysis paralysis and ensures that the assessment focuses on the most critical risks. Objectives should be specific, measurable, achievable, relevant, and time-bound (SMART). For example, instead of simply stating "improve security," a SMART objective might be "Reduce the risk of unauthorized access to sensitive data within the IT department by 20% within the next 12 months." Documenting these objectives will help track progress and demonstrate the value of the assessment. Consider factors like regulatory compliance, business continuity, and employee safety when determining the scope. A poorly defined scope can lead to a superficial assessment, failing to uncover critical vulnerabilities.
Section 2: Asset Identification and Valuation
The cornerstone of any risk assessment is a thorough inventory of assets. These assets encompass everything that has value – physical, digital, intellectual property, and human capital. Asset identification should be comprehensive, encompassing not only tangible items but also intangible assets like reputation and customer trust. Valuation is equally important. This doesn't necessarily require a precise monetary value, but rather an understanding of the asset's importance to the organization. Consider factors like data sensitivity, business disruption potential, and regulatory requirements when assigning values. A simple asset inventory table can be created, listing each asset with its description, location, and estimated value. Regularly updating this inventory is essential to reflect changes in the organization's holdings. Don't underestimate the value of human capital – employee training, security awareness programs, and the potential for insider threats all require careful consideration.
Section 3: Threat Identification
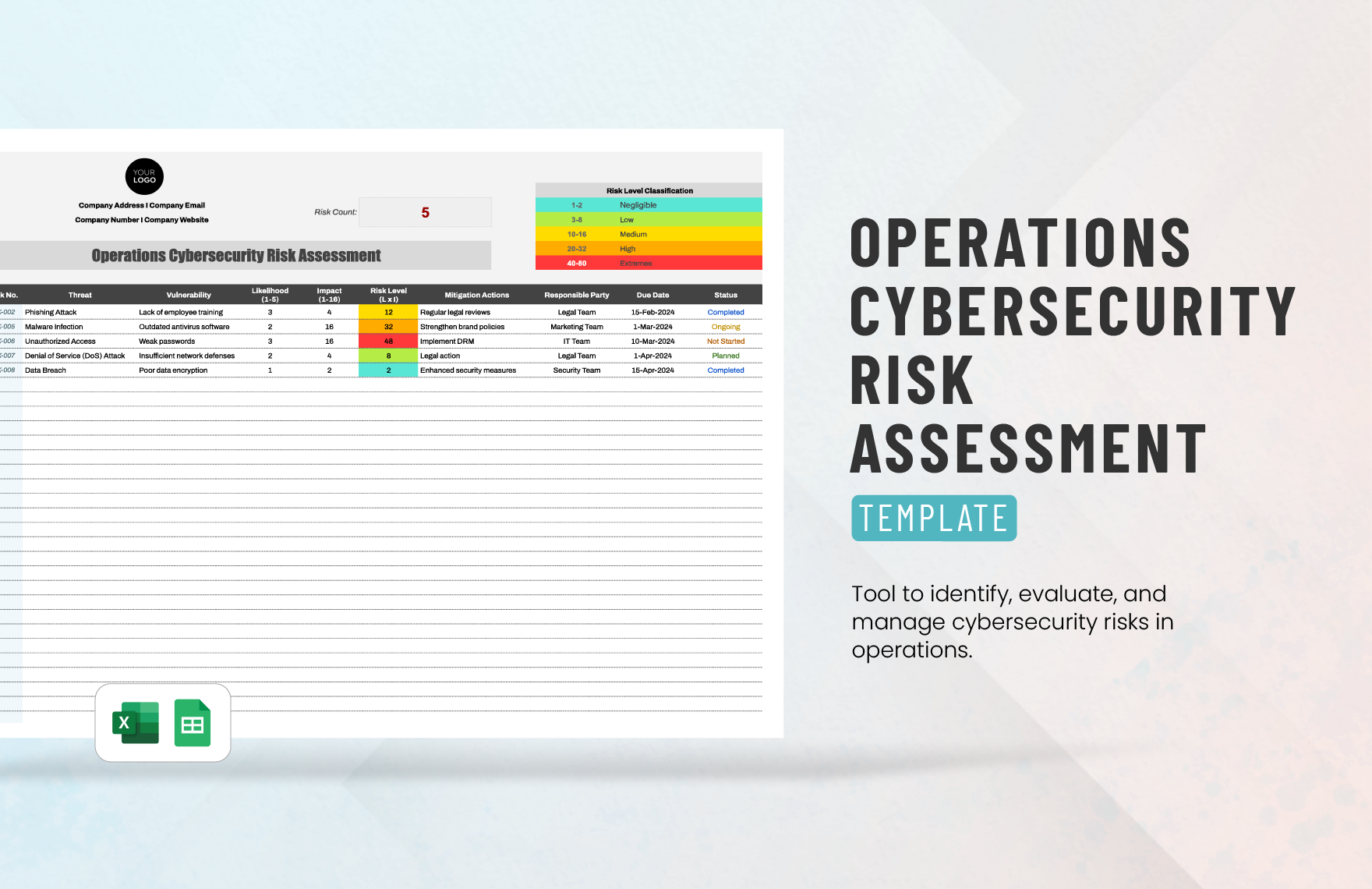
Once assets are identified, it's time to identify potential threats. Threats are the potential causes of harm to an asset. Threat identification should consider both internal and external factors. Internal threats originate from within the organization, such as disgruntled employees, negligent staff, or security breaches. External threats originate from outside the organization, such as cyberattacks, natural disasters, and criminal activity. A threat matrix, visually representing the likelihood and impact of each threat, is a valuable tool for prioritizing risks. Common threat categories include malware, phishing, social engineering, physical theft, and insider threats. Researching industry-specific threats is also crucial. Threat intelligence feeds can provide valuable insights into emerging threats and vulnerabilities. Remember to consider the likelihood of each threat occurring – a high-likelihood threat requires immediate attention.
Section 4: Vulnerability Assessment
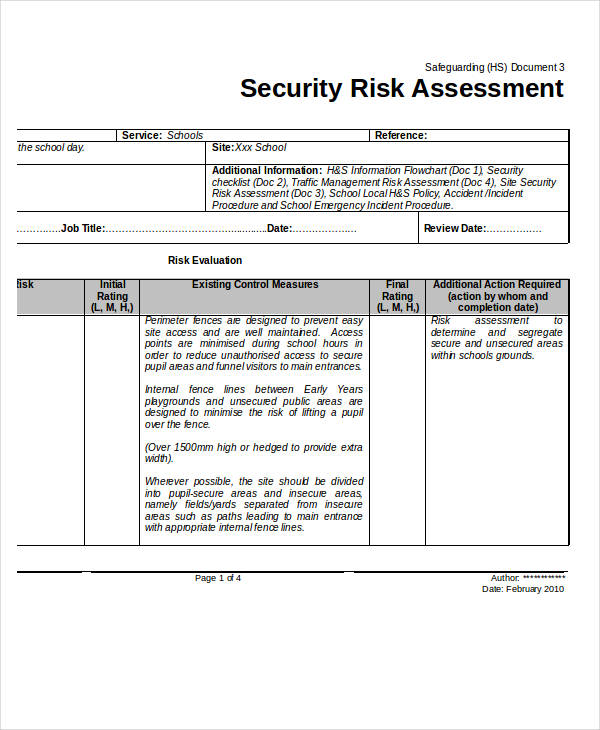
Vulnerabilities are weaknesses in an asset that could be exploited by a threat. Vulnerability assessment involves identifying weaknesses in systems, processes, and controls. This can be achieved through a variety of methods, including vulnerability scanning, penetration testing, and security audits. Vulnerability scanning tools automatically identify known vulnerabilities in systems and networks. Penetration testing simulates real-world attacks to assess the effectiveness of security controls. Security audits involve reviewing policies, procedures, and controls to ensure they are adequate. A thorough vulnerability assessment should identify both known and unknown vulnerabilities. Prioritize vulnerabilities based on their potential impact and likelihood of exploitation. Consider the attack surface – the areas of the organization that are most exposed to potential threats.
Section 5: Risk Analysis and Prioritization
After identifying threats and vulnerabilities, it's crucial to analyze the risks associated with each. Risk analysis involves evaluating the likelihood and impact of each threat exploiting a vulnerability. A risk matrix, typically a 3x3 matrix, is commonly used to visually represent risks. The matrix plots likelihood against impact, allowing for prioritization of risks. High-likelihood, high-impact risks require immediate attention. Low-likelihood, low-impact risks may be monitored but are not prioritized for immediate action. Consider using qualitative or quantitative methods for risk assessment. Quantitative methods, such as Monte Carlo simulations, can provide more precise risk estimates. Documenting the rationale behind risk prioritization is essential for effective communication and decision-making.
Section 6: Risk Mitigation and Control Measures
Once risks have been assessed, it's time to develop mitigation strategies. Mitigation involves taking steps to reduce the likelihood or impact of a risk. Common risk mitigation controls include implementing security policies, strengthening access controls, patching vulnerabilities, and providing security awareness training. Technical controls include firewalls, intrusion detection systems, and antivirus software. Administrative controls include security awareness programs, background checks, and incident response plans. The chosen controls should be proportionate to the risk. Consider the cost-effectiveness of each control. Regularly review and update the risk mitigation plan to ensure it remains effective. Don't underestimate the importance of a layered security approach – combining multiple controls is generally more effective than relying on a single solution.
Section 7: Reporting and Documentation
A comprehensive Risk Assessment Report Template is essential for documenting the findings and communicating them to stakeholders. The report should include a clear summary of the assessment process, identified risks, prioritized mitigation strategies, and recommendations for improvement. It should also include supporting documentation, such as vulnerability scan reports, penetration test results, and policy reviews. The report should be tailored to the audience, providing relevant information for decision-makers. Consider using a standardized format for reporting to ensure consistency and clarity. Regularly review and update the report to reflect changes in the organization's environment. A well-documented report provides a valuable record of the risk assessment process and facilitates continuous improvement.
Conclusion
Physical security risk assessment is a continuous process, not a one-time event. A well-structured Risk Assessment Report Template provides a framework for systematically identifying, analyzing, and mitigating risks. By proactively addressing vulnerabilities and implementing appropriate controls, organizations can significantly enhance their physical security posture and protect their assets. Investing in a robust Risk Assessment Report Template is an investment in the long-term security and resilience of your organization. Remember that security is a journey, not a destination. Continuous monitoring, assessment, and improvement are essential for maintaining a strong security posture. The key to success lies in understanding your organization's specific risks and implementing targeted mitigation strategies. Don't hesitate to seek expert advice when needed – a qualified security consultant can provide valuable insights and support. Ultimately, a proactive approach to physical security risk assessment is a critical component of a comprehensive security strategy.

0 Response to "Physical Security Risk Assessment Report Template"
Posting Komentar